Secure your facility, streamline building access, and monitor who goes where—all in one comprehensive system. Whether you need a simple keycard solution or advanced biometrics, we’ve got you covered.
Choose the reader that fits your environment without compromising security. Our lineup spans wired models for maximum credential flexibility, wireless units for quick, cable-free deployment, and full-featured video intercom stations that combine access control with visitor engagement. No matter which you select, each device integrates seamlessly with FACES2 for consistent management and real-time monitoring across your entire facility.

Supports a wide range of credentials, including PIN, QR code, smart card, smartwatch, and mobile phone. Features a weather sealed housing for indoor and outdoor operation.

Wire-free installation with long-life batteries. Authenticate via smart card, smartwatch, or mobile phone.
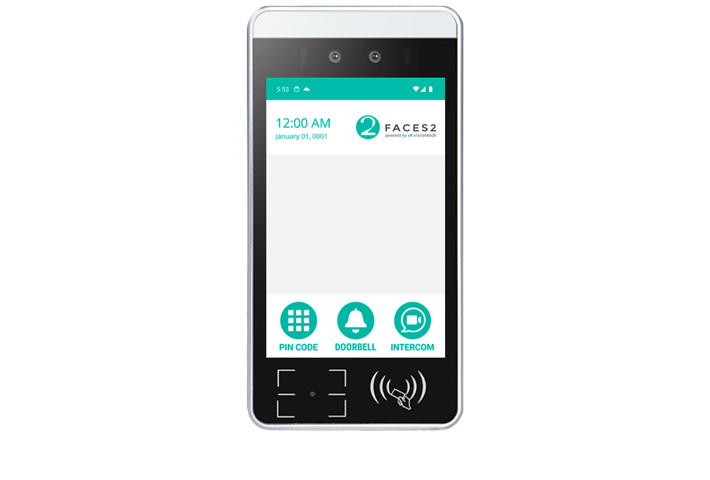
Includes every authentication option offered by our readers plus adds HD video calling, face-match verification with liveness check, and on-screen health questionnaires for seamless visitor screening.
Flexibility is at the core of our access control platform. From biometrics to mobile credentials, you can mix and match the methods below to balance convenience with security, tailor authentication to each user group, and meet evolving compliance requirements, all managed through one unified system.


High-performance access controller for managing doors, readers, and system integration at enterprise scale.
Learn More
Compact and efficient device for handling small-scale access control with full feature compatibility.
Learn More
Expand your setup by connecting up to 16 RS-485 devices for streamlined control and communication.
Learn More
Extend coverage and boost reliability for Matter devices across larger spaces with seamless and secure connectivity.
Learn MoreOur platform supports multiple smart card options to match your security and compatibility needs, whether you’re reading the legacy credentials your staff already carry or deploying advanced NTAG DesFire and JCOP cards with strong encryption. Whatever you choose, each card type integrates seamlessly with FACES2 to deliver fast, reliable and secure authentication.
With our unique design and controller decryption, we can read most client legacy access cards, ensuring seamless integration with existing legacy systems.

Advanced security with AES-128 encryption, secure messaging, and rapid transaction speeds, ensuring robust data protection, reliability, and operational efficiency.
Dual interface Java cards with advanced cryptography, enhanced encryption, and robust anti-tampering mechanisms for secure data storage and communication.
Every facility has distinct security requirements. We work alongside you to build a solution that fits precisely, whether you are protecting a single office door or deploying a large-scale, multi-site network. Choose on-premises, cloud, or hybrid hosting, and connect our platform to your existing applications through a fully documented API for seamless data exchange and centralized management.